이름 : Tanesha
이메일 :
[email protected]
문의내용 :
Onion Dark Website
It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
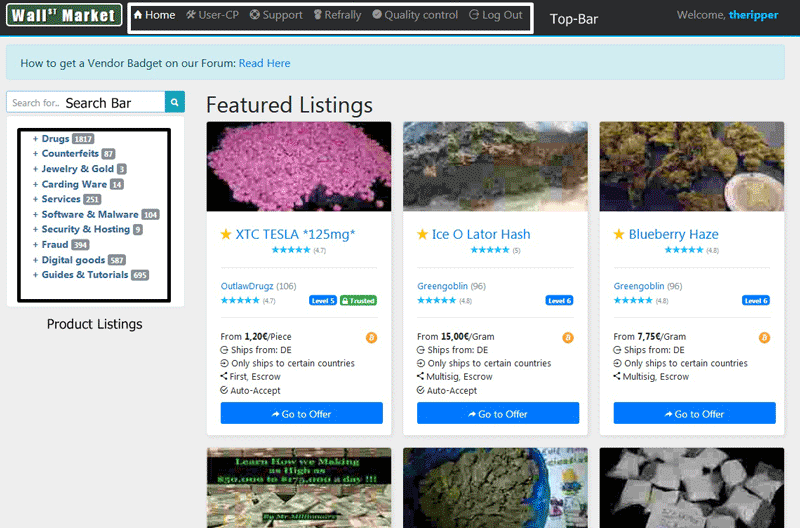
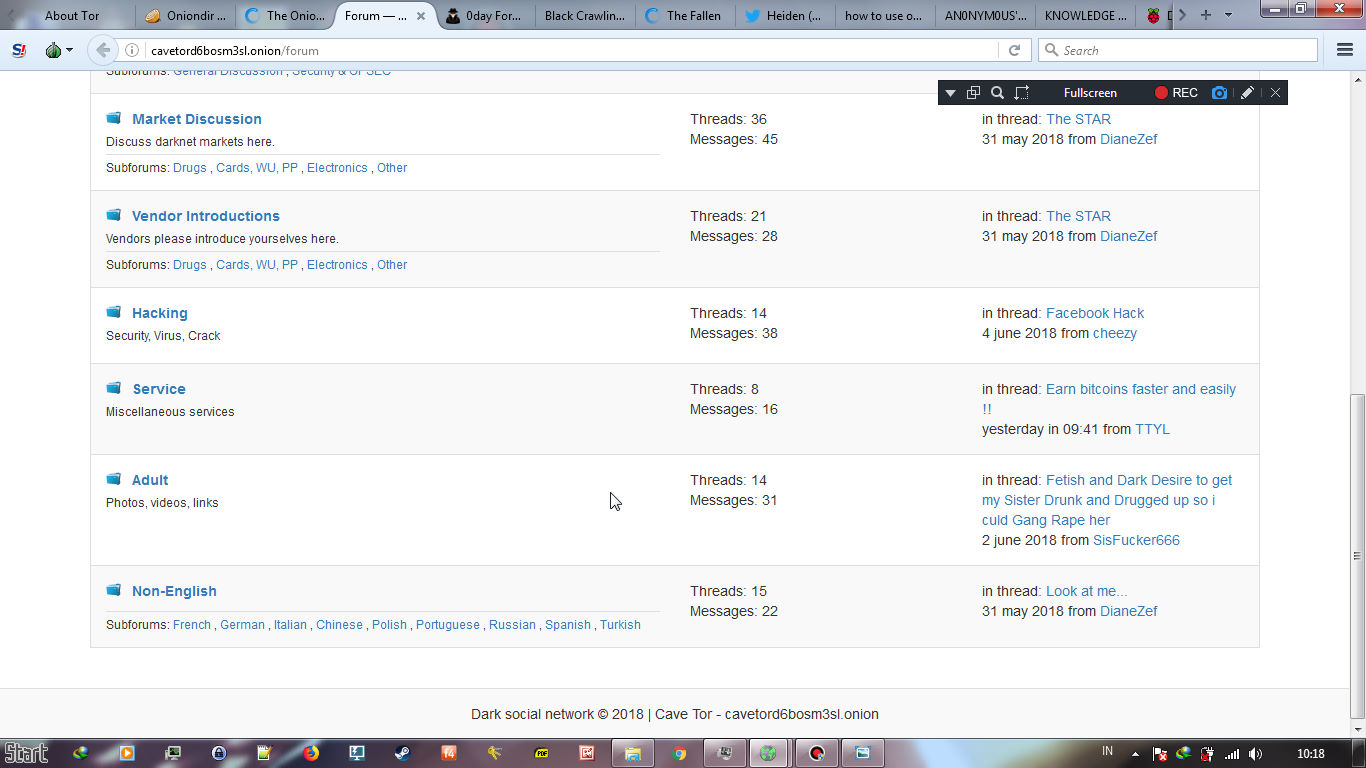
Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and darknet market sites public keys involved. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. Specifically, the I2P darknet market is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
The Unseen Layers of the Network
One of the most popular ways to get around the dark web is not to use a search engine at all. Onion sites are "crawled" and added to the list provided their "robots.txt" file permits it, and if it is not on their blacklist of sites with abuse material. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, dark web darknet market urls or any middleman, knowing who the other is. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Tor allows you to circumvent these restrictions and get access to worldwide news, such as the BBC website shown below.
Most imagine the internet as a sleek, glassy surface—a place of instant connection and polished interfaces. But beneath that surface lies a substratum, a tangled root system of data and darknet market websites discourse. To access it, one doesn't dig down, but rather, peels back. This is the realm some call the onion dark website, a term that perfectly captures its essence: layered, complex, and requiring specific tools to unveil.
More Than a Marketplace
Facebook’s onion mirror allows people to access it in countries that block the platform, allowing people to connect across digital borders. The CIA’s onion site allows users to securely report threats or suspicious activity, especially in regions where online surveillance is common. To access them, copy and paste the hyperlinks provided into the Tor browser.
We strongly recommend connecting to a VPN before you open any dark web links. However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. It provides an .onion URL and an interface for you to manage your Tor site easily.
It is often used when researchers want structured exploration instead of purely keyword-ranked results. That model supports brand monitoring, leak keyword tracking, and other repeatable threat-intelligence tasks. DarkSearch became publicly visible by 2019 and stands out for treating dark web discovery as a monitoring problem.
Popular myth reduces these spaces to digital black markets. While those exist, the reality is far more nuanced. An onion dark website is often a simple, text-heavy forum for darknet market marketplace political dissidents in oppressive regimes. It is a library of rare, censored books. It is a drop box for whistleblowers, protected by layers of encryption that mimic the skin of its namesake vegetable. Each site is a hidden layer, a private chamber in a vast, decentralized castle with no single gate.
The Architecture of Anonymity
How does it work? The "onion" refers to The Onion Router (Tor) network. Your request for a site is wrapped in layers of encryption—like an onion. It is then passed randomly through several volunteer-run computers around the globe, each one peeling back a single layer of encryption only to know where to send it next. The final layer is peeled at the exit node, revealing the destination. This process obscures the user's origin and the site's location, creating a powerful, though not absolute, veil of anonymity.
A Garden of Contradictions
Navigating this space is a study in contrasts. The technology, born from military research for secure communication, now shelters both the heroic and the heinous. One can find communities dedicated to cybersecurity research and open-source intelligence sharing on the same network that hosts unsavory bazaars. This is the central paradox of the onion dark website: it is a tool, and its morality is dictated entirely by the hand that wields it. The anonymity that protects a journalist also shields a criminal.
A Necessary Shadow
In an age of pervasive surveillance and corporate data harvesting, the existence of these hidden layers is increasingly seen as a critical check on power. They are a testament to the internet's original, anarchic spirit—a space beyond the easy reach of censors and advertisers. Whether one views it with fear or fascination, the onion dark website ecosystem forces a crucial question: in a connected world, what is the price of total transparency, and is a right to digital shadows not also a fundamental freedom?
The network's deepest layers remind us that not all valuable things crave the light. Some truths, some conversations, and some forms of liberty must be wrapped tight, passed through trusted hands, and accessed only by those who know how to peel.